- Veröffentlichung:
02.03.2021 - Lesezeit: 5 Minuten
Bogus security through vulnerability scans: Why Pentesting Abandonment Costs Billions
The Green Sign at the bottom right of the taskbar, the animated checkmark in the update history: The increased awareness in terms of IT security has long since arrived in the mainstream – both among consumers and in the professional sector. But how resilient is this supposed security?
It is considered perfectly normal to rely on the status messages of the antivirus software you use. However, the trend of green status is particularly worrying in the professional IT sector: more and more companies are relying on vendor updates together with a reputable appliance to protect them from hostile takeover. This leaves a large attack surface for hackers: Because without prophylaxis, you only treat symptoms, never the cause.
Business leaders, IT strategists and operations managers shy away from penetration testers for valid reasons: It’s uncomfortable to be really scrutinized. One’s own status quo is called into question. When a team of young IT experts reveals the systems of a global corporation in less than an hour – who would want to put their hand in the fire with their supervisor?
But times are changing. Also, with the global Covid-19 pandemic and the evolution to a world where given certainties can become the past on the same day, companies of all sizes are realizing that the safe as-is state no longer exists – it must be put to the test again and again. This is precisely why the hour of professional, strategic pen testing will come in 2021. Experienced experts who know what makes hackers and blackmailers tick can now make all the difference.
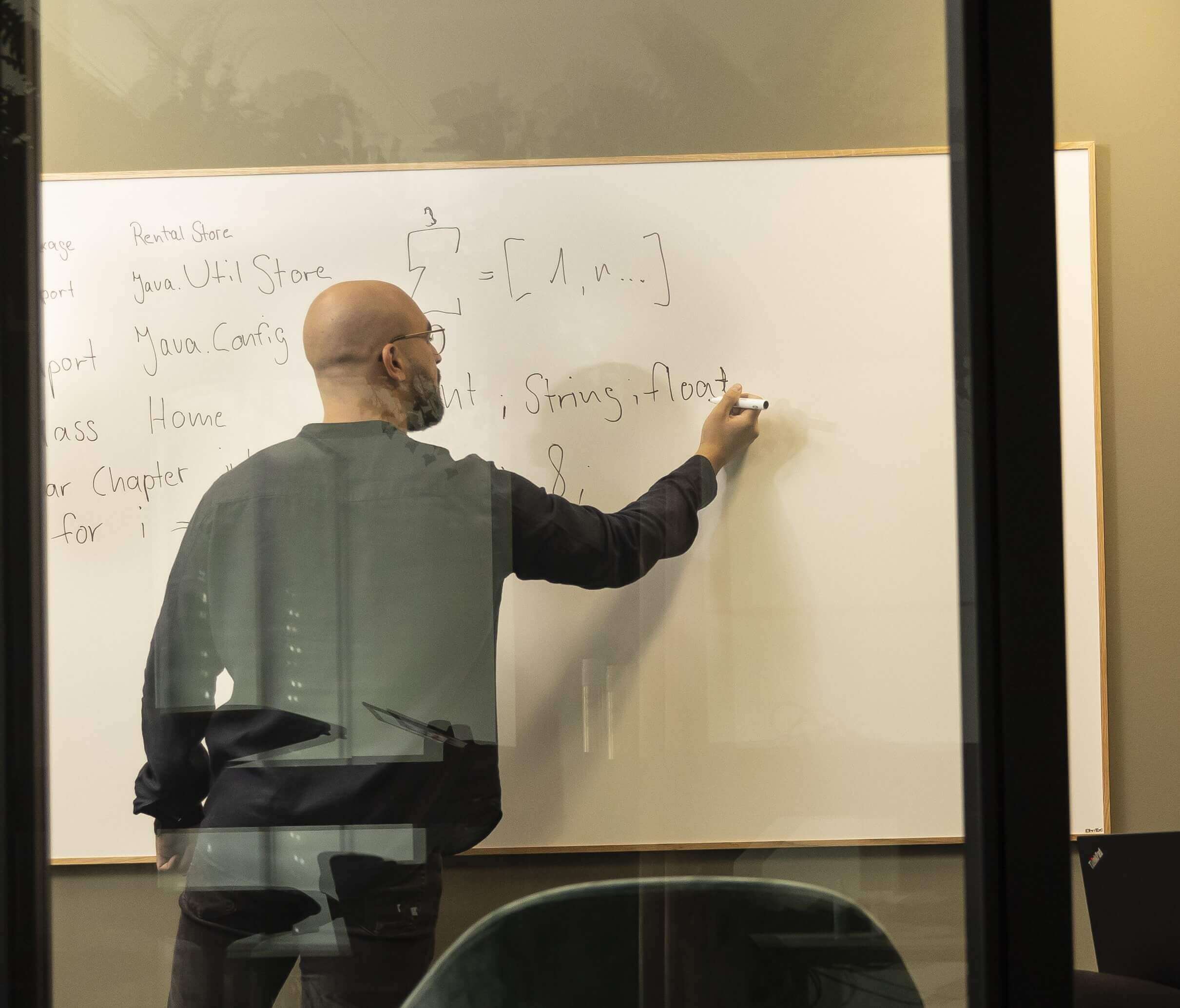
First of all, it is necessary to jointly determine the nature of the test. It shouldn’t be about finding out what’s wrong, what’s not right, or what’s not competent – it should be about consistent learning from the partnership between IT strategists and pentesters. This can be done in a variety of ways: From the consistent safeguarding of one’s own security and resilience strategy to the joint training of one’s own personnel, planning is already half the success story here. The goal should be to enable the company to meet the privacy-by-design requirements, which are also required by law, as early as the planning phase of new IT systems.
In the next steps of preparation, the scope, content and timeframes as well as the involvement of stakeholders and contacts will be clarified. Already at this point, the support within the own organization can be strengthened and anchoring knowledge transfer can succeed in a structured way. Not only IT experts, but also architects and application developers are called upon to participate. Companies achieve the highest benefit when they also include areas that were not previously counted as IT: Product development, manufacturing, support and customer service are today often just shells without IT, which have a high degree of dependency on information technology due to the de-mechanization of customer products to digital product portfolios.
During implementation, it is first necessary to consider the business context of the company and thus the economic value, the position as well as the supply chains. Anything that a hacker can detect and perceive from the outside is the first target of an attack – the web store, the customer portal or online banking. This is where IT strategists and IT operations need to work together: The high number of web applications, cloud services and hybrid network structures must be examined and further developed holistically. Every weak point is an opportunity – not only for the optimization of technology but also for strategic positioning vis-à-vis the market and the competition.
There’s nothing good unless you do it – that’s why we’re your strong partner who will pitch in together after a PenTest. Our experts have decades of experience in following up audit reports, deriving technical and organizational measures, and implementing IT requirements. Whether data center, desktop services, web applications or cloud: when it comes to doing, we bring our comprehensive know-how to bear and help companies achieve strategic optimization on their own in the future.
At Ventum Consulting we are sure: Wait and see is the highest risk. Vulnerabilities like ShellShock, BlueKeep and EternalBlue, are proof that putting off security measures can cost companies their existence!
Our expert for you
Author
Daniel Querzola
Former manager at Ventum Consulting and cybersecurity expert